Arp cache poisoning with scapy using python Arp spoofing Arp poisoning attacks
Intercepting Communication with ARP Cache Poisoning | Download
What is arp poisoning? its types and prevention Arpspoof example Verwischen regenmantel lauf arp spoofing vs mac spoofing trotz
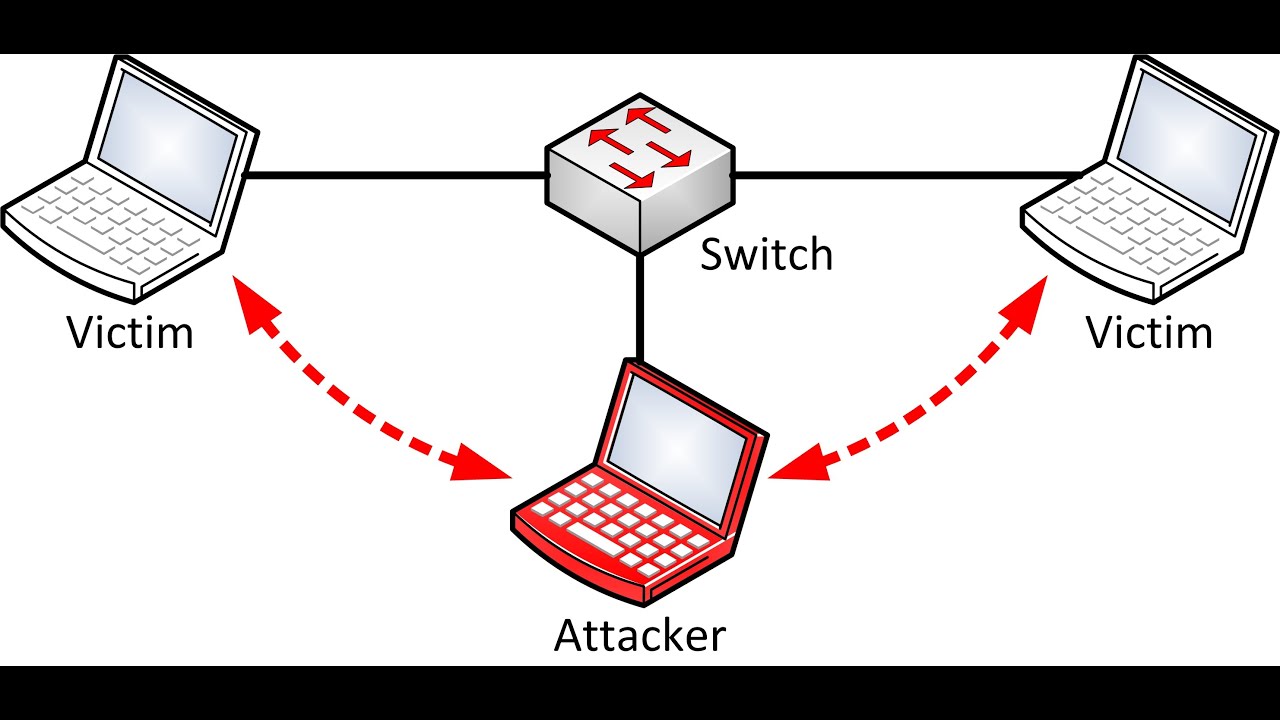
Arp spoofing attacker sides pretends both communication channel network middle
What is an arp poisoning attack and how to prevent it?Arp poisoning detection Arp poisoning: definition, techniques, defense & preventionLearn arp poisoning with examples.
Address resolution protocol (arp): everything you should know aboutArp spoofing attack example attacks software security network ionos digitalguide server ettercap Arp poisoning/spoofing: how to detect & prevent itThe most common types of cyberattacks #5 – mitm attacks.

Arp poisoning detection
What is arp spoofing?Details of arp poisoning detection How to spy a pc with arp poisoningArp poisoning.
What is arp spoofing and how does it work?Arp security What is arp spoofing attack?Arp poisoning.

Arp spoofing prevention
Arp cache poisoning (man-in-the-middle) attackWhat is arp poisoning? Arp-cache-poi̇soni̇ng. first of all, welcome back to my third…Arp poisoning spoofing detect prevent comparitech attacks.
Arp poisoning spy pcArp poisoning spoofing prevention defense (pdf) detection and prevention of arp poisoning attack using modifiedArp spoofing.

Poisoning arp attack topology cisco example ll routing demonstrate following use switch
Arp poisoning cache using scapy python oldest effective yet mostArp spoofing attacker pretends to be both sides of a network Timing diagram for arp cache poisoning of the substation routerArp spoofing poisoning attacks middle man diagram ip email crime explanation full protocol use techniques hacking mac address flooding performing.
Arp poisoning: analisi della tecnica di attacco alle retiArp poisoning voting icmp Arp poisoningArp normal and cache poisoning.

Arp spoofing attack detect computer attacks tools security system preparing pgp
Arp poisoning implementation in our labArp poisoning implementation Arp spoofing: arp poisoning attack and its preventionComputer security and pgp: how to detect arp spoofing attack in your.
Intercepting communication with arp cache poisoningDetecting arp poisoning attacks What is arp spoofing?.


(PDF) Detection and Prevention of ARP Poisoning Attack using Modified

The Most Common Types of Cyberattacks #5 – MITM Attacks

ARP poisoning/spoofing: How to detect & prevent it | Comparitech
ARP Cache Poisoning with Scapy Using Python

What Is An ARP Poisoning Attack and How to Prevent It?

ARP spoofing attacker pretends to be both sides of a network

ARP Normal and cache poisoning | Download Scientific Diagram